Does the process of obtaining a security clearance feel as grueling and unending as Frodo Baggins’s quest to destroy the One Ring of Power? Does the idea of “reciprocity” in the security realm seem like a dream from the best of all possible worlds? Do clear and definitive security regulations seem to be as accessible as stone tablets inscribed in dead languages hidden in forgotten ruins in Middle Earth?
If you answered “yes” to any of these questions, you’re not alone. Before the OPM data breach, the average wait time for a clearance was 1-3 months for a Confidential or Secret and 4-8 months for a Top Secret. Since the breach, times have doubled on average, and as FSO at Tesla, I have seen individuals trapped in security limbo for three+ years without getting final eligibility. The slow pace of this process poses obvious challenges to individuals with a legitimate need to know who require access to classified and control marked information to do their jobs.
In 2016, OPM brought on an additional 400 employees and pledged to hire 200 more in 2017 to address the backlog of approximately 700,000 investigations. Unfortunately, the contract to hire those additional investigators in 2017 is being contested. An additional cause for pessimism is that investigators in the field have told me that individuals unfortunate enough to have started their investigation shortly before or around the breach were essentially shuffled into a pile. As new cases arrived, new casefiles were just piled on top of those stalled investigations, pushing those poor souls even further down into what can appear to be an unending purgatory of stalled background investigations.
If you are fortunate enough to be granted final eligibility, the next challenge is the lack of actual reciprocity between agencies. If you aren’t familiar with the idea of reciprocity, allow me to explain. Clearance types and levels vary from agency to agency, background investigation processes are unique to each agency, and some agencies, such as CIA, have their own system that is separate from OPM’s. The result is that completing the arduous background investigation process and being granted final TS eligibility does not mean every agency will accept that clearance and provide access to the same level of data.
This is where reciprocity comes in. Ideally, agencies work together when employees work between them. For example, a worker might have a clearance issued by DoD but need to shuffle over to do some work at the State Department. The state would then assess the DoD clearance and issue a reciprocity clearance for its own agency. State essentially accepts the DoD clearance for use on its system.
Despite claims of reciprocity, however, the security world is much better at paying lip service to the idea that practicing it. As with information sharing in general, the challenge is to overcome individuals’ and agencies’ tendency to want sharing or reciprocity to go one way, only to their benefit. A common understanding of information sharing is “you give me your information; I’ll keep mine.” Similarly, reciprocity often manifests as the attitude that other agencies should respect your clearance determinations but not vice versa.
So what is to be done? It is idealistic to envision a single unified system with consistent clearance levels and controls that are treated consistently across the Interagency. Barring one all-encompassing security system to rule them all, though, a high-side, the centralized repository could provide controlled access to clearance information and up-to-date, standardized security regulations, procedures, and processes across agencies. A single site with applicability across all agencies could provide huge time savings over the long run. Similarly, actual reciprocity between agencies would save significant time and help ensure that people with an actual need-to-know are given the access they need to do their jobs.
Reciprocity in the broadest sense is vital to effective information sharing of any kind. In the security realm, they need to know must be balanced with the need to control information, but currently, the desire for tighter security often comes at the expense of legitimate and necessary sharing of information. A perfect balance may be impossible to achieve—there might not truly be that One Ring in the security realm—but a secure information sharing system for interagency security information would be a huge positive step in that direction.
Related posts
When Big Tech Is Not the Answer—Why Small Businesses Get More Done

Afghanistan Is Finally Holding Elections—While the Taliban Gobbles Up Territory

The Geospatial Data Act of 2017: A Necessary Step Forward, with One Major Flaw

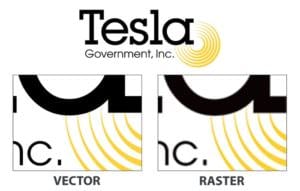
Vector vs. Raster: What Do They Mean and Which Should I Use?